[Security: Entra ID] How To Secure Guest User Access & SPO OTP Retirement

This blog post explains how to secure guest user access and highlights a few practical takeaways for securing your M365 tenant while managing guest user permissions. Settings regarding external sharing, configuring CA policies, creating access reviews and many more will be covered in this blog! We also take a look at the upcoming changes to SharePoint OTP and the retirement of this feature.
1. External Collaboration Settings
The first step is to configure the external collaboration settings in Microsoft Entra ID. With external collaboration settings we can define the following:
- Guest user access: How external user can access our internal resources;
- Guest invite settings: Who they can invite to our tenant;
- External user leave settings: What guest are allowed to do;
Collaboration restrictions: Which domains are allowed or blocked.
Follow these steps to configure this:
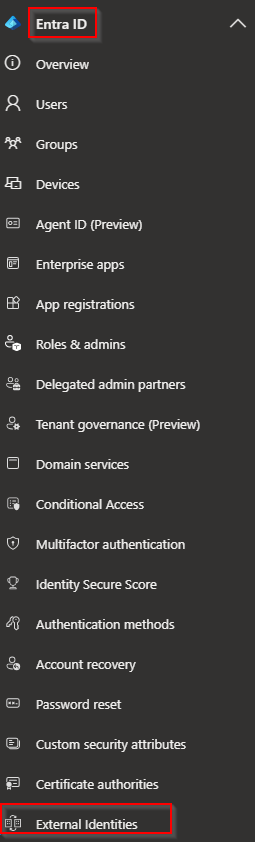
- Go to the Entra admin center (entra.microsoft.com)
- Navigate to Entra ID -> External Identities
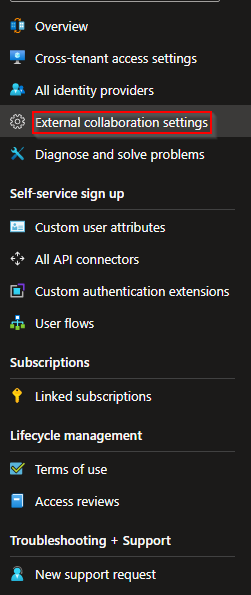
Next, select External collaboration settings
From this settings menu, it is now possible to configure collaboration settings. I recommend configuring the following:
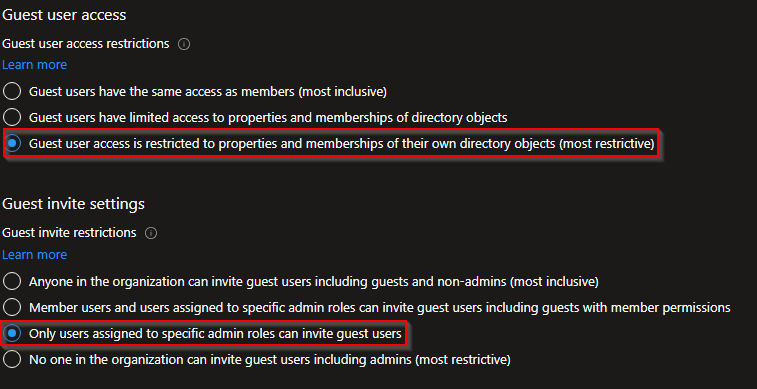
*Note: these settings are the most secure to configure but you may need to adjust these settings afterwards as none of your users are able to invite a guest member to their documents. If so you can choose to adjust this "guest invite settings" to "Member users and users assigned to specific admin roles can invite guest users including guests with member permissions".
As you could see I've set the following:
- Guest user access is restricted to properties and memberships of their own directory objects (most restrictive);
- Only users assigned to specific admin roles can invite guest users.
2. External Sharing
In the SharePoint admin center we can configure some external sharing settings. By default Microsoft sets the sharing settings fully open so we need to change these settings. Let's go over to our SharePoint admin center and configure these changes. I will explain two options that you could configure, both with pro and cons:
2.1 Sharing Settings
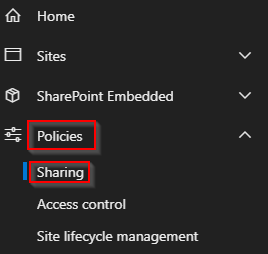
- Go to the SharePoint admin center (%tenantname%-admin.sharepoint.com)
- Navigate to Policies -> Sharing
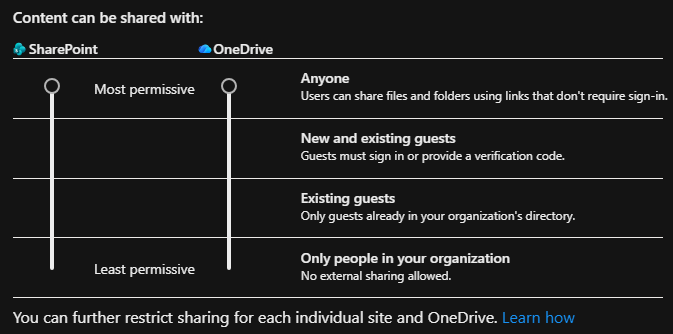
From the sharing page we can see that the default sharing is allowed for everyone. This means that if someone shared a document, this document will be available to everyone that has the link to this document by default.
As you can see from the screenshot above, the default isn't something that we want to have in our environment. Now there are two defaults you may want to set. My personal recommendation is setting sharing to only existing guests and limit sharing to specific domains as followed:
*Note: this also means that you will need to create guest account yourself/make a automation for this.
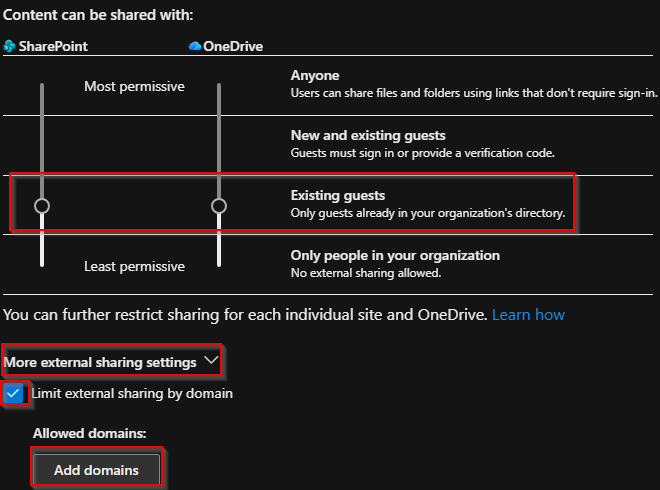
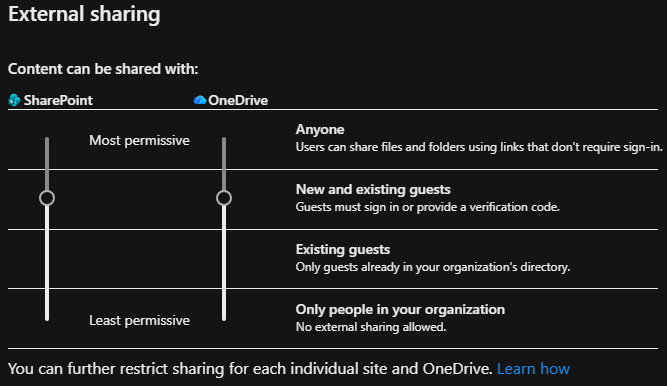
As a write above ,these settings will be most restrictive. Another option will be setting this to "New and existing guests".
Pros:
Both limitations are set to reduce your anonymous exposure;
Both options forces external users to authenticate;
Depending on your configuration guests will receive a verification code in their e-mail or a guest user will be created in your tenant (B2B).
Cons:
The second option will be less secure as users can invite their guests themselves without having to submit a ticket for creating a guest user;
without limiting domains users can invite every organization/domain they want to share their documents with.
Next we want to set the following options:
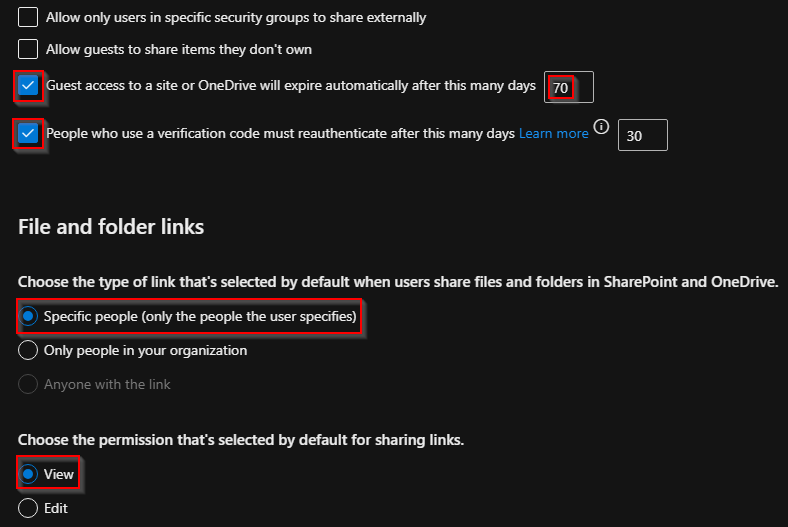
Guest access expires: with this setting configured, after 70 days the access to that specific file/folder/site will be automatically removed;
Verification code: set to 30, so users need to re authenticate after 30 days.
Specific People: let your users select their contacts they want to share their documents with. This way you force to select the correct organizations/persons;
Choose permission: select View. Most of the time users only need to have view rights. This will also overcome any oversharing regarding edit rights.
2.2 Block Downloads On Unmanaged Devices (SPO Method)
Now there are a couple of options to restrict unmanaged devices to download and edit organization documents. In this blogpost I will only discuss the method using SharePoint Online. Another option is to configure Defender for Cloud Apps.
From the SharePoint admin center browse to "Policies" -> "Access control" -> select "Unmanaged devices"
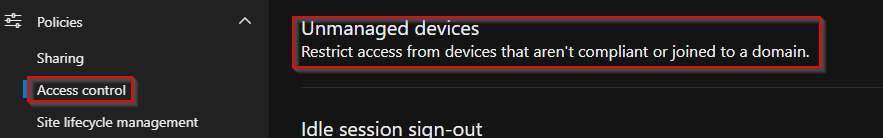
From the Unmanaged devices menu, select "Allow limited, web-only access"
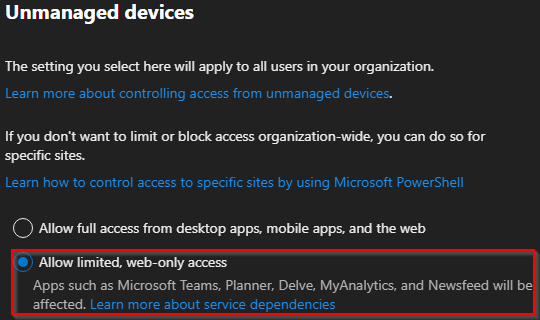
After you save this setting, there will be two auto generated CA policy's saying it will require Entra (hybrid) joined devices and it needs to be compliant with SharePoint Online as target resource. The other policy will be a app-enforced restriction for browser access. With this second policy the user will be unable to download any file. Also this policy is scoped to SharePoint Online.
3. B2B Integration And Retirement SPO OTP (August 2026)
Starting from May 2026, SharePoint one-time passcode (OTP) will be retired. Until now, it was possible to either configure SharePoint OTP (a user shares a document with a guest and the guest receives a one-time passcode to view the document) or set up a B2B integration using PowerShell (EnableAzureADB2BIntegration). From May 2026 onward, new external sharing invitations and authentication will use Microsoft Entra B2B instead of SharePoint Online OTP. Starting from July 2026 the option to disable a B2B integration will be removed.
3.1 So, How Do I Act On This?
There are a couple of takeaways:
Existing B2B guests:
Existing B2B guests will still be able to login.
External guests without B2B Integration:
Documents shared after the SPO change:
Guest accounts will automatically be created using the B2B Integration;
The autentication will use the B2B e-mail OTP. Be sure that this has been enabled! I will post the steps below.
Documents shared before SPO change:
SharePoint OTP will work until July 2026. After this month users will receive access denied until they are created as guests using B2B.
So there are two options you could choose from. From my recommendation I always create the guest user myself. Another option is to let the users re share their documents, folder or site, so the guest account will be created. All auto created guest users can be found in Entra ID.
3.2 How To Enable email OTP
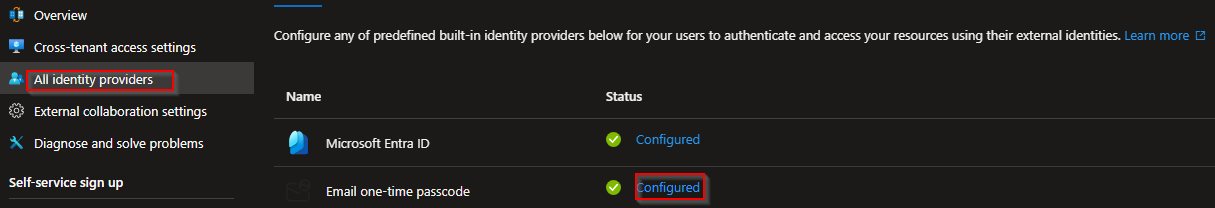
If your organization relies on e-mail OTP authentication, you should check the External ID settings in Entra:
Follow these steps to check this:
- Go to the Entra admin center (entra.microsoft.com)
- Navigate to Entra ID -> External Identities
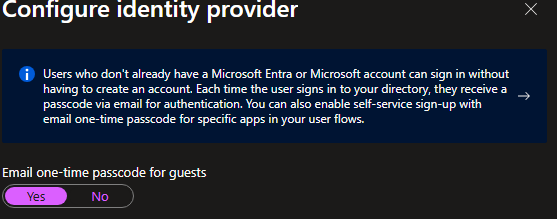
Next select "All identity providers" -> Email one-time passcode -> select "Configured" and set this to Yes
4. Require And Configure MFA
We want our guest users to connect securely to our environment, so we're going to configure MFA for our guest users. Passkey/FIDO2 isn't supported for B2B and guest users yet, but with a few tweaks we could do the trick. First let setup a Conditional Access policy so our guest user needs to have MFA registered.
Follow these steps to configure this:
- Go to the Entra admin center (entra.microsoft.com)
- Navigate to Entra ID -> Conditional Access -> select "Policies"
- Select "New policy"
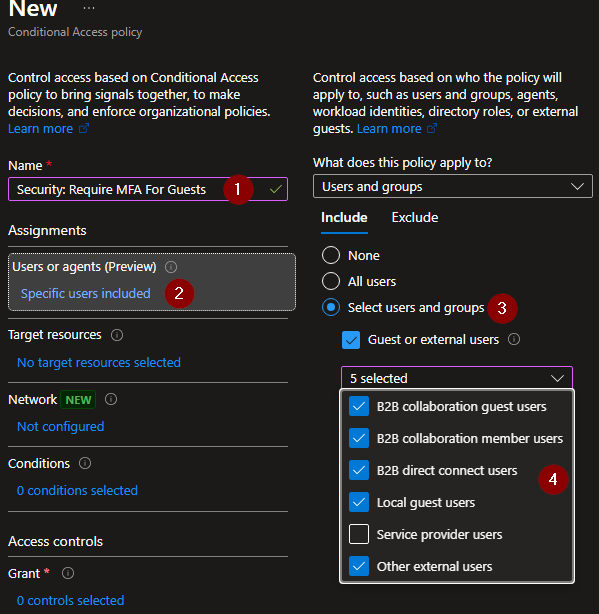
A new CA policy config will appear. From this screen we want to configure the following:
- Users or agents
Select your external users as below;
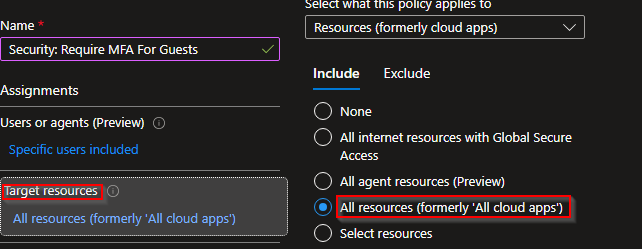
- Target resources
All resources (formerly 'All cloud apps');
- Grant
Select Require multifactor authentication.

Please keep in mind that this will prompt your guest users to setup MFA once they login to your tenant. Most organizations already have MFA in place, so these guest users may start asking why they need to do this again. In the next section I will discuss a bit more on that.
4.1 So How About Passkey/Double MFA?
If a user already has a MFA/FIDO2/Passkey registred in their own organization, they will be double prompted for a MFA when connecting to your organization.
To avoid this you could configure "Cross tenant access settings" for the organizations you work most with. When configured, your tenant will accept the other organization regarding its configured MFA.
To configure this we have to browse back to our "External Identities" overview. From here we select "Cross-tenant access settings":
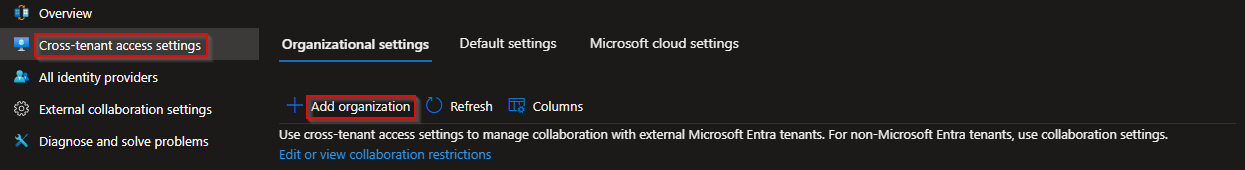
Next, enter the organization name you want to add and select "Add". Now the organization will be listed. From here we select "Inherited from default" found under "Inbound access":
Select "Trust settings" -> "Customize settings" -> select "Trust multifactor authentication from Microsoft Entra tenants"
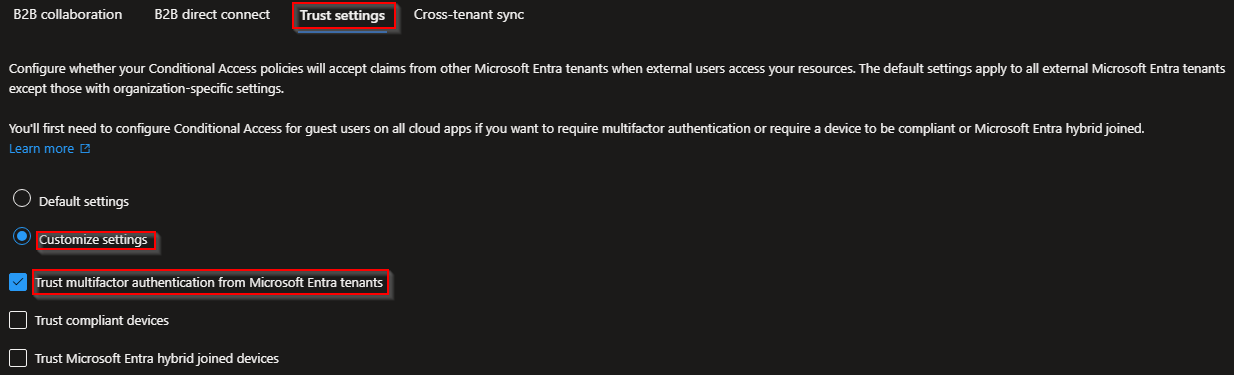
Now the users will be prompted one time instead of having registering another MFA / do double authentication (own tenant and yours).
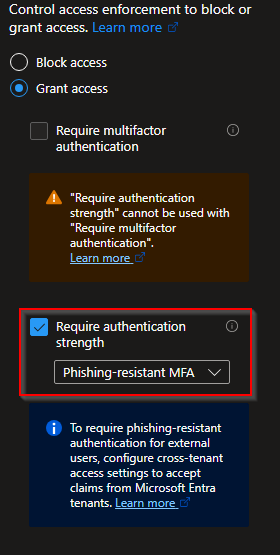
If an organization is using FIDO2/Passkey you could also use this option. For example, an organization is using Passkey and has access to your tenant, then you could create another CA policy that requires strong authentication instead of MFA. By this the user only needs to authenticate with their FIDO2/Passkey.
5. Access Reviews (Review Guest Access)
Access reviews is a great option when you want to revoke access to guest users that haven't been signed in for a while. Please note as this is a Entra P2 license, but if you have this please continue reading!
How to config access reviews:
- Go to the Entra admin center (entra.microsoft.com)
- Navigate to ID Governance -> Access reviews
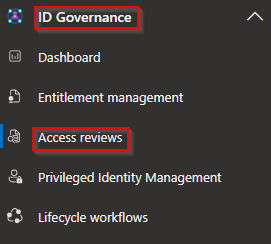
Select "New access review". On the next screen select "Review access to a resource type".
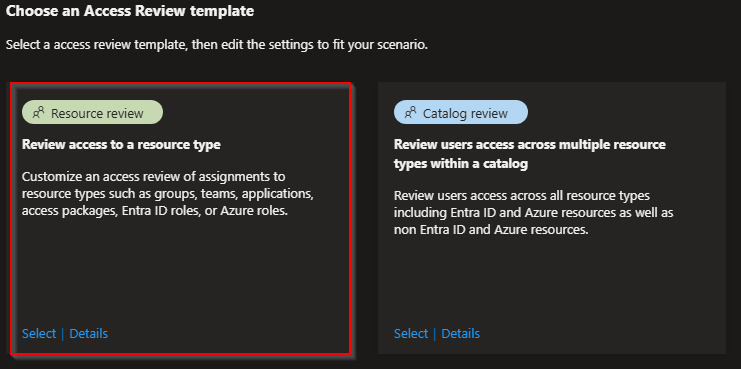
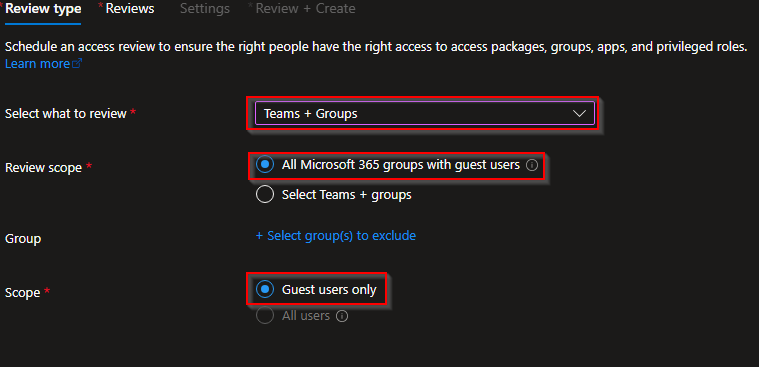
On the "Review type" screen we select the following:
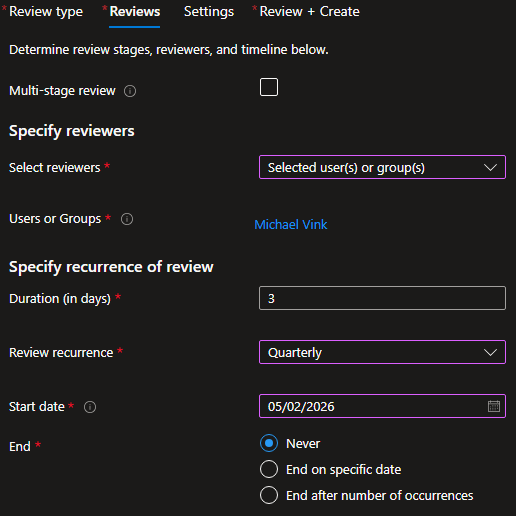
Next we have "Reviews" where we can configure our revievers. This could be for example a security specialist or another colleague. My recommendation on this is setting the recurrence to "Quarterly" as this extends 90 days inactivity.
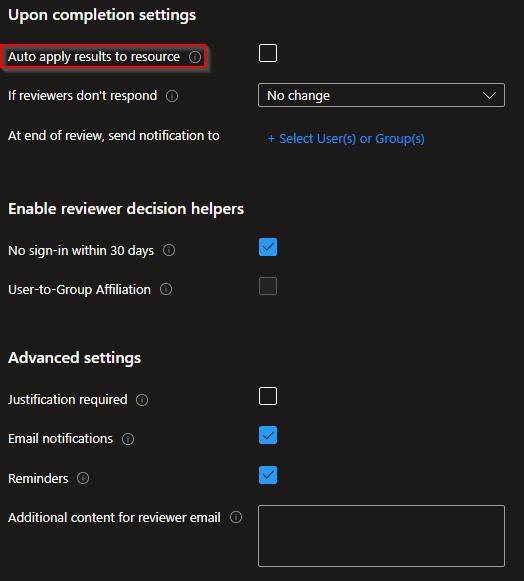
When we select Next, we see some settings that we could change. You can configure and apply these settings by your own needs. You could choose to "Auto apply results to resource". With this settings it will automatically remove the access to the resource or group. If you first want to have a quick look at the logs, you should leave this option unchecked.
*Note: This access review won't disable or delete a guest user. It will only notify you that this person has no sign-in within 30 days. It will only remove access to the resource/group(s).
6. Wrap-Up
More and more guests will connect to your organization, which is perfectly fine. Securing guest access and regularly reviewing their sign-ins over time is one of the essential configurations to set up in any organization. Of course, this should be done without introducing too many “issues”, such as double MFA prompts. This blog post provides a baseline of what can be configured in an organization. Always make sure to test these settings thoroughly before moving them into production.