[Security: Entra ID] Passkeys, Windows Hello And Phishing-Resistant Sign-Ins (Public Preview)

In this blogpost we're going to talk about configuring a Passkey profile so you can sign-in to Entra-protected cloud resources using Windows Hello! A great new feature that will come to your tenant from mid-March through mid-April 2026. This new feature sets a new standard for unmanaged devices, shared endpoints and BYOD as these will now be able to use your organizations policy regarding phishing-resistant passwordless authentication.
1. Great, But What Does This Feature Mean?
In my blog from last month I wrote about setting up Passkey profiles for your tenant and about configuring a device bound Passkey profile.
Now Microsoft just announced that you will be able to create and use this device bound Passkey to sign-in to Entra protected resources using the Windows Hello container (fingerprint, pin or face)!
*Note: device sign-in on a unmanaged device is not supported using this method.
2. What Are The Requirements?
First there are some things that need to be clarified:
Windows Hello for Business remains recommended for Entra joined/registered endpoints;
This Passkey profile method can be used on unmanaged (shared, personal) devices. This won't effect your corporate Entra joined/registered devices;
Multiple Entra accounts can be used on the same Windows device registering their own passkey;
Users cannot register a passkey on Windows if a Windows Hello for Business credential already exists for the same account and container. This limitation may no longer apply once the user has more than 50 total credentials across passkeys (FIDO2), Windows Hello for Business, and Mac Platform Credentials.
The following requirements are needed:
Passkey profile with device-bound enforcement (as explained in my previous blog);
Adding Key restrictions (AAGUIDs);
CA policy needs to be configured correctly (strong-authentication), so your environment is allowing the use of Passkey authentication.
3. How Do I Configure This?
*Note: The following guide can be followed when you have enabled Passkey as a authentication method described in my previous blog. Also always be sure to test this out first before bringing this to production.
The first thing we want to do is browse to the Entra Admin Center:
- Go to the Entra admin center (entra.microsoft.com)
- Browse to Entra ID -> Authentication methods

From the authentication methods select "Policies".
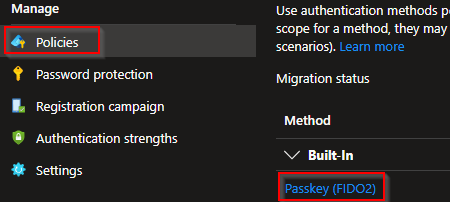
Select Passkey (FIDO2). From this new page select "Configure".
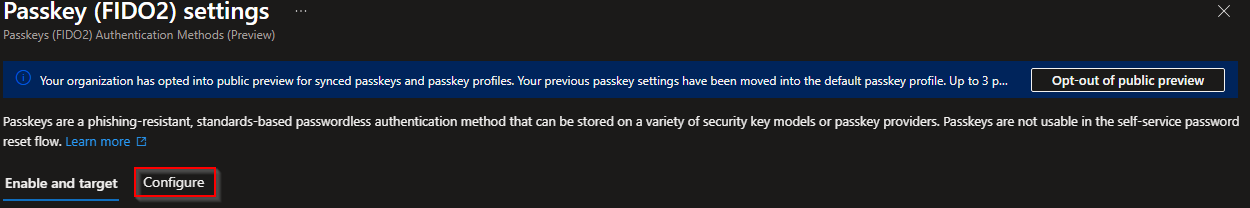
Select "Add profile (preview)". We cannot use our default profile because "attestation enforcement" needs to be disabled for this type of configuration.

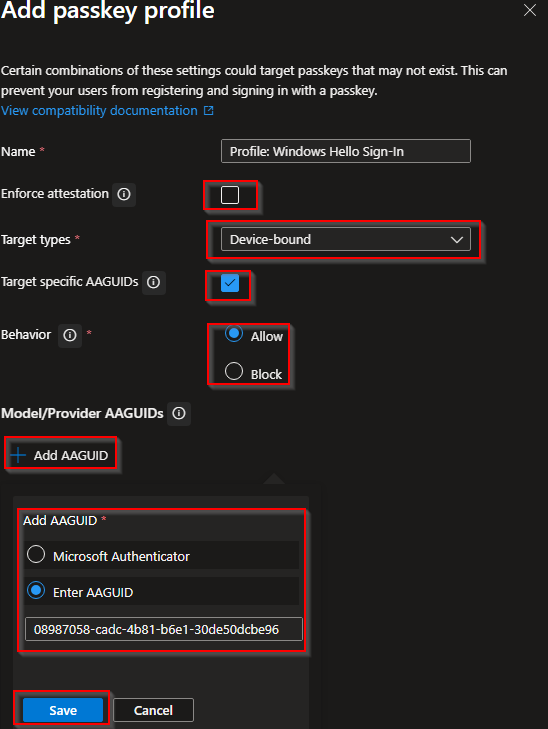
Start giving this profile a name and select and add the following:
- Enforce attestation: Disabled
- Target types: Device-bound
- Target specific AAGUIDs: Enabled -> Behavior: Allowed
Select "Add AADGUID" and add the following:
- Windows Hello Hardware Authenticator: 08987058-cadc-4b81-b6e1-30de50dcbe96
- Windows Hello VBS Hardware Authenticator: 9ddd1817-af5a-4672-a2b9-3e3dd95000a9
- Windows Hello Software Authenticator: 6028b017-b1d4-4c02-b4b3-afcdafc96bb2
If all settings are configured correctly you should see the following. Also take note of the information bar confirming that you can only use this as a device-bound passkey:

Head back to your Passkey(FIDO2) authentication method and start targeting the users/groups that you want to be able to use this new Passkey profile.

